When Microsoft heralded Windows 11, people were curious what the term TPM 2.0 actually means. And this module is one of the major requirements of the Windows 11 operating system and it is a way of storing and creating encryption keys in hardware.
SEE ALSO: How to Install Windows 11 on an Unsupported Device
The TPM is a definition which illustrates a distinctive processor device to shield encryption keys storage and data security. It is a secure crypto-processor that protects a computer through an integrated cryptographic key. For instance, this chip can save keys for encrypting a hard drive via a Bitlocker technology.
This module serves as a security signal to your device to fend off malicious software or hackers from getting access to your data. The definition is executed either as a distinct software emulation or physical processor based on BIOS firmware. And most of the present-day Intel and AMD chipsets motherboards come with the TPM 2.0 software emulation.
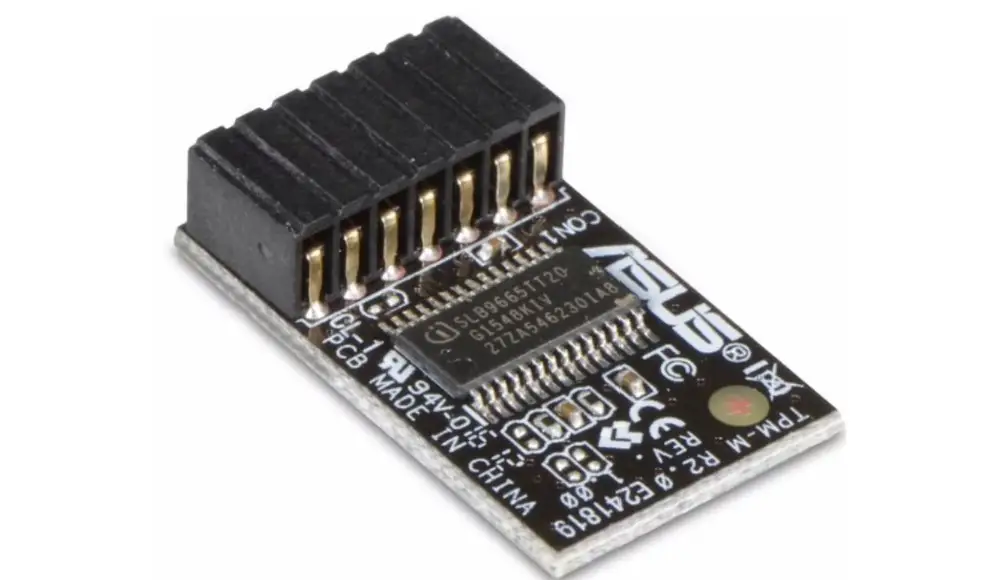
However, numerous motherboards are compatible with installation of the distinct physical chips which appear as a little panel with a unique connector. These kinds of panels with chips are uncommon, so makers of motherboards roll them out definitively for their hardware.
So, if you need to get a definite module, check out whether it supports your motherboard before purchasing it.
If your PC doesn’t come with the TPM 2.0, one means to get it is to purchase a module that supports your motherboard. Users will need to find out the model of your motherboard and observe if the producer ever launched a supported Trusted Platform Module (TPM).
We have hardware and software securities. Hardware security deals with cryptographic keys which are impossible to alter except the hacker knows the right keys. The TPM 2.0 features the hardware security that has built-in root-of-trust as well as it interacts with other security systems in your computer. And the other security systems could be Microsoft Windows Hello facial recognition, fingerprint sensor, etc. Also some apps such as Chrome, Firefox and Outlook make use of TPM
And Software security is a potent way to hinder hackers from accessing your device. Based on software is amenable, that is the coding can be altered. So there is a possibility that white hat hackers can access your device.
SEE ALSO:
How to Improve Windows 11 Performance
How to Run Android Apps on Windows 11
How to Use Speech Recognition to Interact with Apps in Windows 11



Comments